To deploy a new instance of NSX-T into an environment with two isolated tenants, you need to follow these steps:
Log in to the NSX Manager UI with admin credentials. The default URL is https:// .
Navigate to System > Fabric > Nodes > Edge Transport Nodes and click Add Edge VM.
Enter a name and an optional description for the edge VM. Select the compute manager, cluster, and resource pool where you want to deploy the edge VM. Click Next.
Select the deployment size and form factor for the edge VM. For this task, you can select Medium as the size and VM as the form factor. Click Next.
Select the datastore and folder where you want to store the edge VM files. Click Next.
Configure the management network settings for the edge VM. Enter a hostname, a management IP address, a default gateway, a DNS server, and a domain search list. Optionally, you can enable SSH and join the edge VM to a domain. Click Next.
Configure the transport network settings for the edge VM. Select an N-VDS as the host switch type and enter a name for it. Select an uplink profile from the drop-down menu or create a new one by clicking New Uplink Profile. Map the uplinks to the physical NICs on the edge VM. For example, map Uplink 1 to fp-eth0 and Uplink 2 to fp-eth1. Optionally, you can configure IP assignment, MTU, or LLDP for the uplinks. Click Next.
Review the configuration summary and click Finish to deploy the edge VM.
Repeat steps 2 to 8 to deploy another edge VM for redundancy.
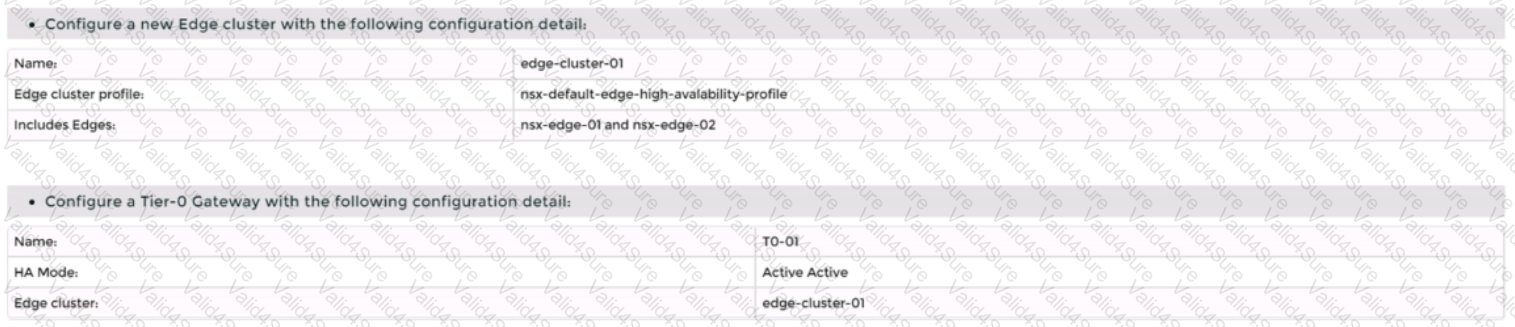
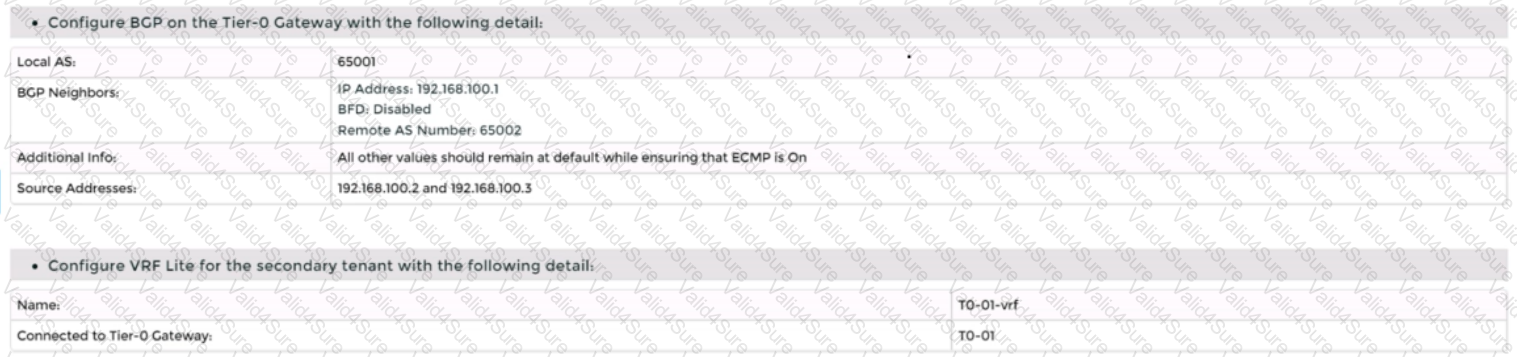
Navigate to Networking > Tier-0 Gateway and click Add Gateway > VRF.
Enter a name and an optional description for the VRF gateway. Select an existing tier-0 gateway as the parent gateway or create a new one by clicking New Tier-0 Gateway.
Click VRF Settings and enter a VRF ID for the tenant. Optionally, you can enable EVPN settings if you want to use EVPN as the control plane protocol for VXLAN overlay networks.
Click Save to create the VRF gateway.
Repeat steps 10 to 13 to create another VRF gateway for the second tenant with a different VRF ID.
Navigate to Networking > Segments and click Add Segment.
Enter a name and an optional description for the segment. Select VLAN as the connectivity option and enter a VLAN ID for the segment. For example, enter 128 for Tenant A’s first uplink VLAN segment.
Select an existing transport zone from the drop-down menu or create a new one by clicking New Transport Zone.
Click Save to create the segment.
Repeat steps 15 to 18 to create three more segments for Tenant A’s second uplink VLAN segment (VLAN ID 129) and Tenant B’s uplink VLAN segments (VLAN ID 158 and 159).
Navigate to Networking > Tier-0 Gateway and select the VRF gateway that you created for Tenant A.
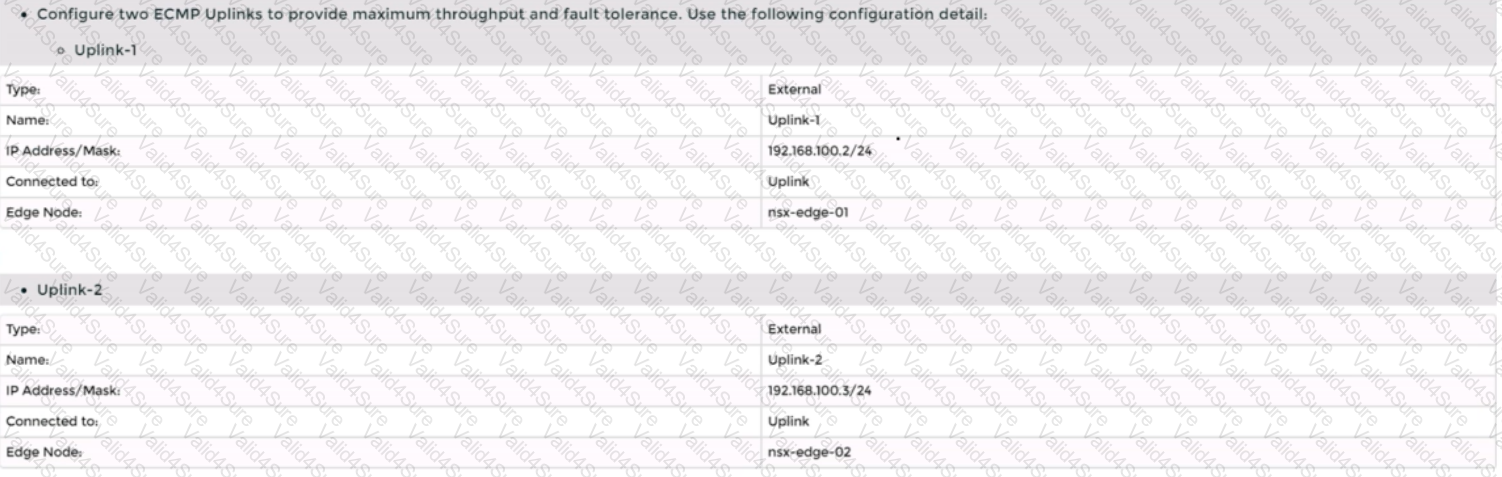
Click Interfaces > Set > Add Interface.
Enter a name and an optional description for the interface.
Enter the IP address and mask for the external interface in CIDR format, such as 10.10.10.1/24.
In Type, select External.
In Connected To (Segment), select the VLAN segment that you created for Tenant A’s first uplink VLAN segment (VLAN ID 128).
Select an edge node where you want to attach the interface, such as Edge-01.
Enter the Access VLAN ID from the list as configured for the segment, such as 128.
Click Save and then Close.
Repeat steps 21 to 28 to create another interface for Tenant A’s second uplink VLAN segment (VLAN ID 129) on another edge node, such as Edge-02.
Repeat steps 20 to 29 to create two interfaces for Tenant B’s uplink VLAN segments (VLAN ID 158 and 159) on each edge node using their respective VRF gateway and IP addresses.
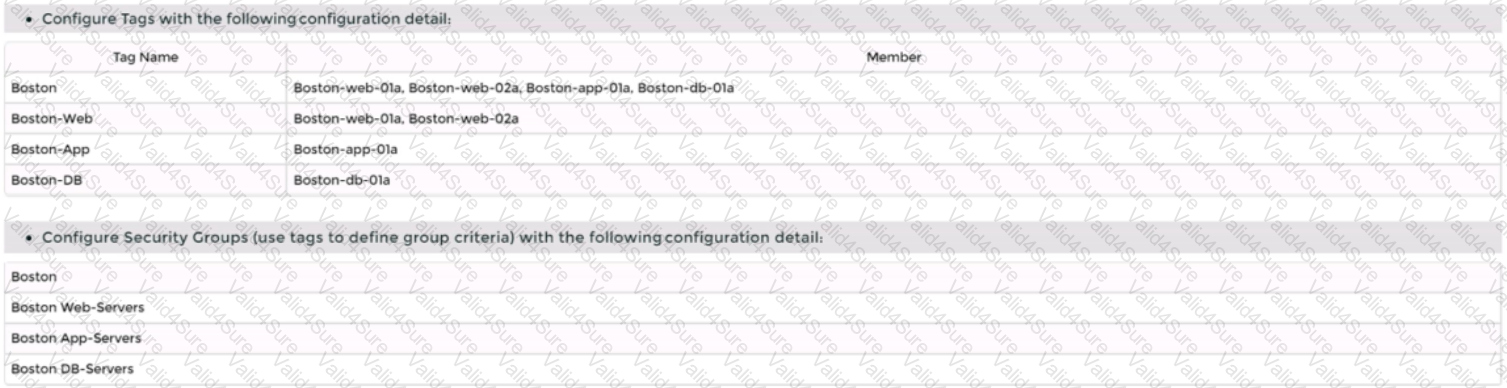
Configure BGP on each VRF gateway using NSX UI or CLI commands12.You need to specify the local AS number, remote AS number, BGP neighbors, route redistribution, route filters, timers, authentication, graceful restart, etc., according to your requirements34.
Configure BGP on each physical router using their respective CLI commands56.You need to specify similar parameters as in step 31 and ensure that they match with their corresponding VRF gateway settings78.
Verify that BGP sessions are established between each VRF gateway and its physical router neighbors using NSX UI or CLI commands . You can also check the routing tables and BGP statistics on each device .
You have successfully deployed a new instance of NSX-T into an environment with two isolated tenants using VRF Lite and BGP.