1. R1 received DHCP packet and its interface was configured with the DHCP helper address. But we are not sure if R1 forward DHCP packet to R2 or not. 2. If we connect PC directly to R2 then this problem will not appear -> DHCP Server function was configured on R2.
From these facts, the most likely problem is related to Option 82. Maybe R2 ignored DHCP request packets because it was receiving these packets with the giant field set to 0.0.0.0.
By default Cisco IOS devices reject packets with zero “giaddr†and by default Cisco Catalyst switches use “giaddr†of zero when configured for DHCP snooping! Reference: https://blog.ine.com/2009/07/22/understanding-dhcp-option-82
If we can run the “debug ip dhcp server packet†on R2, we may see these messages:
*Feb 22 23:54:57.759: IP: s=0.0.0.0 (FastEthernet0/1), d=255.255.255.255, len 34 4, input feature, MCI Check(64), rtype 0, forus FALSE, sendself FALSE, mtu 0, fw dchk FALSE *Feb 22 23:54:57.759: IP: s=0.0.0.0 (FastEthernet0/1), d=255.255.255.255, len 34 4, rcvd 2 *Feb 22 23:54:57.759: IP: s=0.0.0.0 (FastEthernet0/1), d=255.255.255.255, len 34 4, stop process pak for forus packet
*Feb 22 23:54:57.759: DHCPD: inconsistent relay information. *Feb 22 23:54:57.759: DHCPD: relay information option exists, but giaddr is zero
We are receiving the DHCP packet from R1, source 0.0.0.0, and destination 255.255.255.255 broadcast, but if you notice from the debug output, R2, our DHCP Server, is complaining that the relay information is inconsistent. Option 82, Information Option, is contained in the packet but the GIADDR is zero. The GIADDR stands for Gateway IP Address, which is the IP Address of the relaying agent. The Option 82, Information Option, would then contain the receiving port and hostname of the Relaying Agent by default.
R2 sees the Option 82 information, signalling that the DHCP packet might have been relayed, BUT there is no relaying IP Address. This is the behavior of DHCP Snooping when enabling it on a switch, and since the switchport does not contain an IP Address, since it’s Layer 2, no GIADDR will be added.
Instead, just the Option 82 Information is added and this is the problem we have, but there are options:
1. You could trust all on R2 the DHCP Server, which will cause the server to not be so suspicious: – ip dhcp relay information trust-all – ip dhcp relay information trusted 2. Disable theaddition of Option 82 information on SW: – no ip dhcp snooping information option 3. Trust the port that is receiving the DHCP Discover: – ip dhcp snooping trust
Any of these options will fix our predicament.
[Reference: https://evilttl.com/wiki/DHCP-Snooping, But in the answer choices, we only have 1 correct answer which is the command “ip dhcp relay information trust-allâ€. We checked if we need any “service dhcp…†command on both IOS version 12.4 and 15.1:, , , , Therefore we only have the “service dhcp†command, we don’t have any “service dhcp-relay†command available. But the description of the “service dhcp†command says that it enables both DHCP server and relay agent so this is the best answer left., , , ]

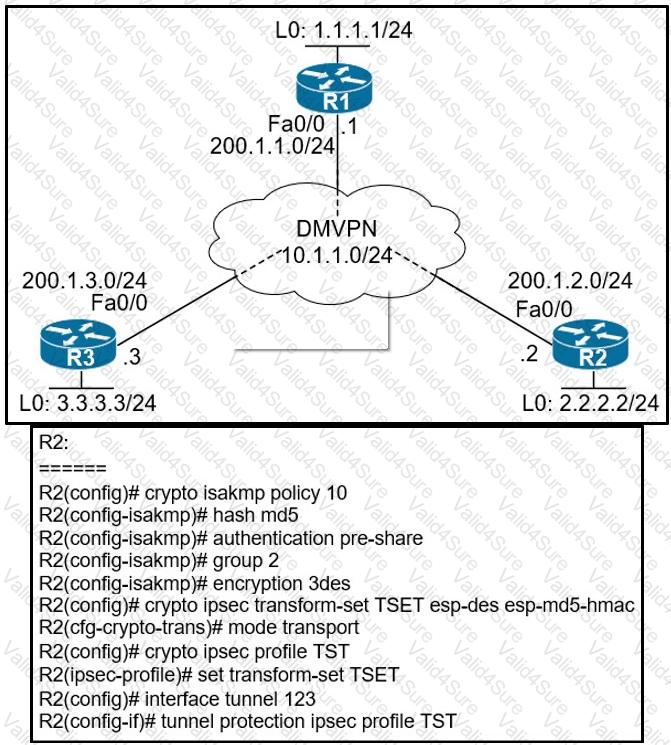
 Diagram Description automatically generated
Diagram Description automatically generated