350-201 Exam Dumps - Performing CyberOps Using Core Security Technologies (CBRCOR)
Question # 25
Refer to the exhibit.
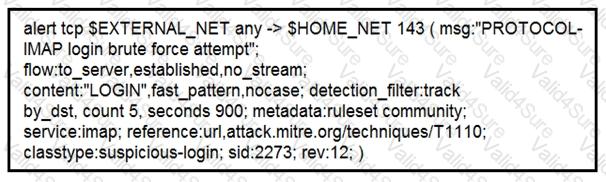
IDS is producing an increased amount of false positive events about brute force attempts on the organization’s mail server. How should the Snort rule be modified to improve performance?
Question # 26
Refer to the exhibit.
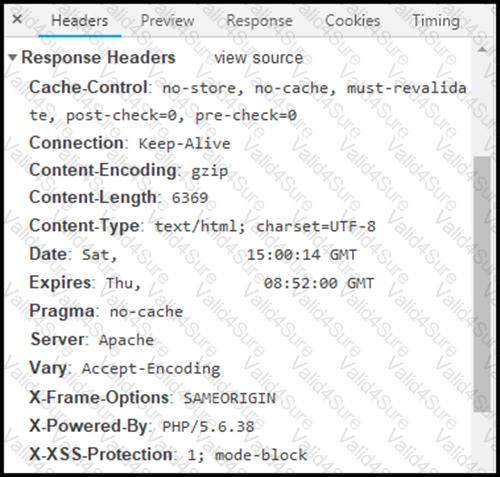
Where are the browser page rendering permissions displayed?