HPE7-A02 Exam Dumps - Aruba Certified Network Security Professional Exam
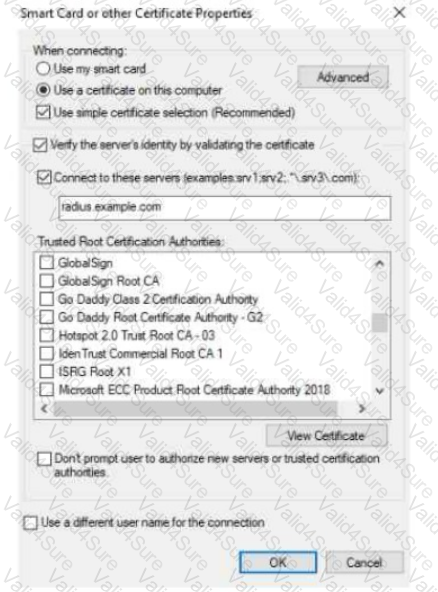
The exhibit shows the 802.1X-related settings for Windows domain clients. What should admins change to make the settings follow best security practices?
A company has AOS-CX switches. The company wants to make it simpler and faster for admins to detect denial of service (DoS) attacks, such as ping or ARP floods, launched against the switches.
What can you do to support this use case?

(Note that the HPE Aruba Networking Central interface shown here might look slightly different from what you see in your HPE Aruba Networking Central
interface as versions change; however, similar concepts continue to apply.)
An HPE Aruba Networking 9x00 gateway is part of an HPE Aruba Networking Central group that has the settings shown in the exhibit. What would cause the
gateway to drop traffic as part of its IDPS settings?
An AOS-CX switch has been configured to implement UBT to two HPE Aruba Networking gateways that implement VRRP on the users' VLAN. What correctly describes how the switch tunnels UBT users' traffic to those gateways?
HPE Aruba Networking Central displays an alert about an Infrastructure Attack that was detected. You go to the Security > RAPIDS events and see that the attack was "Detect adhoc using Valid SSID." What is one possible next step?
You are setting up HPE Aruba Networking SSE to prohibit users from uploading and downloading files from Dropbox. What is part of the process?
A company has AOS-CX switches and HPE Aruba Networking APs, which run AOS-10 and bridge their SSIDs. Company security policies require 802.1X on all
edge ports, some of which connect to APs.
How should you configure the auth-mode on AOS-CX switches?
A company has Aruba APs that are controlled by Central and that implement WIDS. When you check WIDS events, you see a "detect valid SSID misuse" event. What can you interpret from this event, and what steps should you take?