SC-300 Exam Dumps - Microsoft Identity and Access Administrator
Searching for workable clues to ace the Microsoft SC-300 Exam? You’re on the right place! ExamCert has realistic, trusted and authentic exam prep tools to help you achieve your desired credential. ExamCert’s SC-300 PDF Study Guide, Testing Engine and Exam Dumps follow a reliable exam preparation strategy, providing you the most relevant and updated study material that is crafted in an easy to learn format of questions and answers. ExamCert’s study tools aim at simplifying all complex and confusing concepts of the exam and introduce you to the real exam scenario and practice it with the help of its testing engine and real exam dumps
You have an Azure subscription that contains a user named User! and two resource groups named RG1 and RG2.
You need to ensure that User1 can perform the following tasks:
• View all resources.
• Restart virtual machines.
• Create virtual machines in RG1 only.
• Create storage accounts in RG1 only.
What is the minimum number of role-based access control (RBAC) role assignment* required?
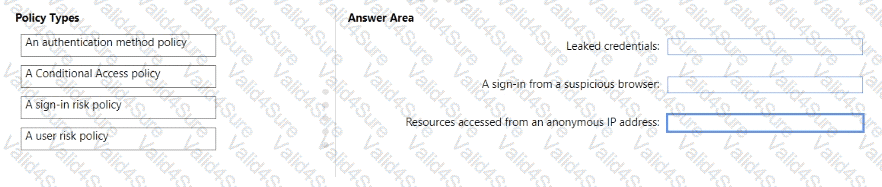
You need to resolve the recent security incident issues.
What should you configure for each incident? To answer, drag the appropriate policy types to the correct issues. Each policy type may be used once, more than once, or not at all. You may need to drag the split bar between panes or scroll to view content.
NOTE: Each correct selection is worth one point.
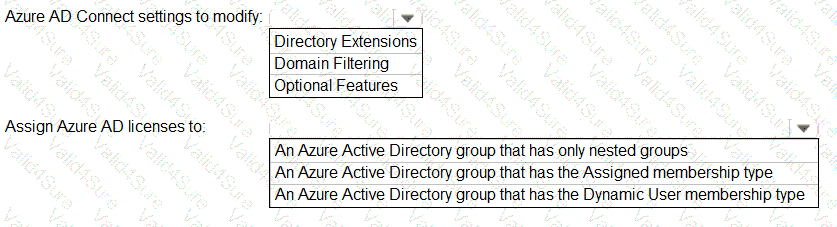
You need to configure the assignment of Azure AD licenses to the Litware users. The solution must meet the licensing requirements.
What should you do? To answer, select the appropriate options in the answer area.
NOTE:Each correct selection is worth one point.
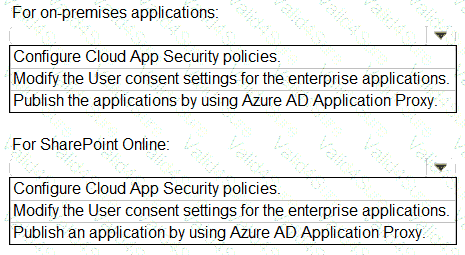
You need to implement on-premises application and SharePoint Online restrictions to meet the authentication requirements and the access requirements.
What should you do? To answer, select the appropriate options in the answer area.
NOTE:Each correct selection is worth one point.
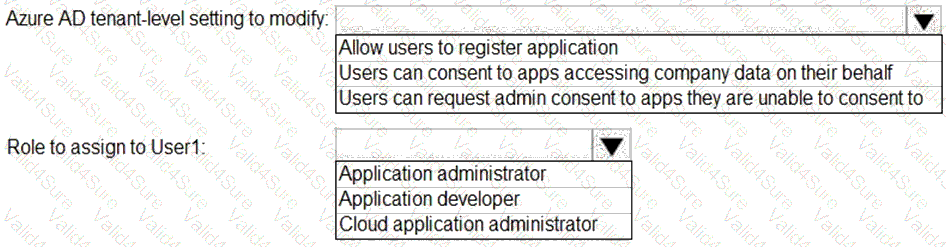
You need to configure app registration in Azure AD to meet the delegation requirements.
What should you do? To answer, select the appropriate options in the answer area.
NOTE:Each correct selection is worth one point.