350-501 Exam Dumps - Implementing and Operating Cisco Service Provider Network Core Technologies (350-501 SPCOR)
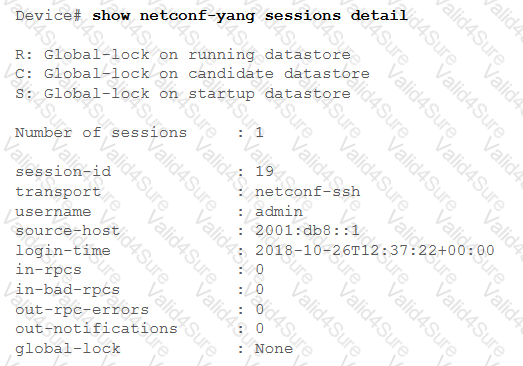
After a possible security breach, the network administrator of an ISP must verify the times that several different users logged into the network. Which command must the administrator enter to display the login time of each user that activated a session?
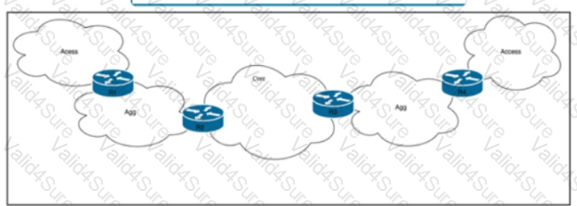
Refer to the exhibit. Tier 1 ISP A purchased several Tier 2 ISPs to increase their customer base and provide more regional coverage. ISP A plans to implement MPLS services in the access layer, with scalability up to 100.000 devices In one packet network and service recovery up to 50 ms. The network architect decided to use different independent IGP and LDP domains and interconnect LSPs that are based on RFC 3107. Which two actions must the network engineer perform to meet the requirements? (Choose two.)
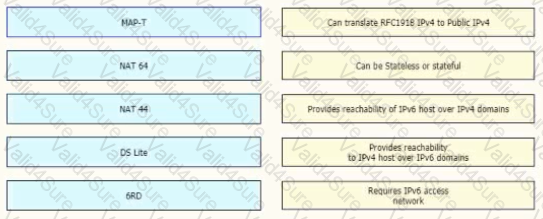
Drag and drop the functionalities from the left onto the target fields on the right.
A company is expanding its existing office space to a new floor of the building, and the networking team is installing a new set of switches. The new switches are running IGMPv2, and the engineers configured them for VLAN10 only. The rest of the existing network includes numerous Layer 2 switches in multiple other VLANs, all running IGMPv3. Which additional task must the team perform when deploying the new switches so that traffic is switched correctly through the entire network?

Refer to the exhibit. A network operator working for a private telecommunication company with an employee id: 7138: 13:414 just added new users to the network, which resides in VLANs connected to routers R1 and R4. The engineer now must configure the network so that routers R1 and R4 share routes to the VLANs, but routers R2 and R3 are prevented from including the routes in their routing tables. Which configuration must the engineer apply to R4 to begin implementing the request?
While implementing TTL security, an engineer issues the PE(config-router-af)#neighbor 2.2.2.2 ttl-security hops 2 command. After issuing this command, which BGP packets does the PE accept?