XK0-005 Exam Dumps - CompTIA Linux+ Exam
Searching for workable clues to ace the CompTIA XK0-005 Exam? You’re on the right place! ExamCert has realistic, trusted and authentic exam prep tools to help you achieve your desired credential. ExamCert’s XK0-005 PDF Study Guide, Testing Engine and Exam Dumps follow a reliable exam preparation strategy, providing you the most relevant and updated study material that is crafted in an easy to learn format of questions and answers. ExamCert’s study tools aim at simplifying all complex and confusing concepts of the exam and introduce you to the real exam scenario and practice it with the help of its testing engine and real exam dumps
A developer needs to launch an Nginx image container, name it Web001, and ex-pose port 8080 externally while mapping to port 80 inside the container. Which of the following commands will accomplish this task?
After connecting to a remote host via SSH, an administrator attempts to run an application but receives the following error:
arduino
Error: cannot open display:
Which of the following should the administrator do to resolve this error?
A Linux administrator is configuring a new internal web server fleet. The web servers are up and running but can only be reached by users directly via IP address. The administrator is attempting to fix this inconvenience by requesting appropriate records from the DNS team. The details are:
Hostname: devel.comptia.org
IP address: 5.5.5.1, 5.5.5.2, 5.5.5.3, 5.5.5.4
Name server: 5.5.5.254
Additional names: dev.comptia.org, development.comptia.org
Which of the following types of DNS records should the Linux administrator request from the DNS team? (Select three).
A systems administrator is tasked with configuring a repository on an RPM-based Linux system. Which of the following need to be reviewed and modified? (Select two).
Which of the following technologies provides load balancing, encryption, and observability in containerized environments?
An administrator is investigating an issue on a Linux-based router where packets enter the machine but are not sent to their destinations in the 10.0.6.0/24 subnet. The administrator inspects the following output from the diagnostic commands:
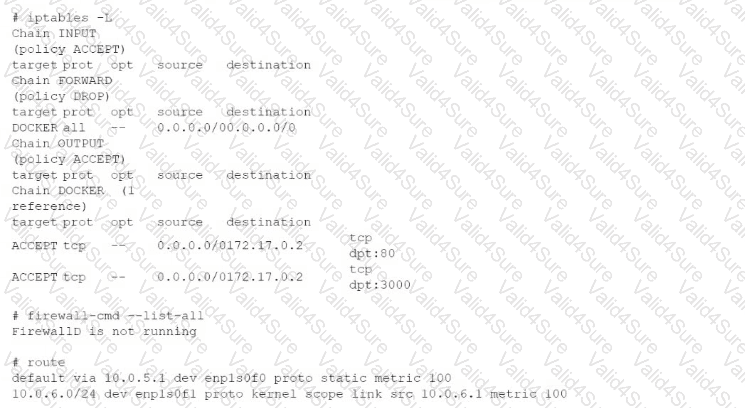
Which of the following commands should the administrator run to enable the routing?
A Linux systems administrator needs to persistently enable IPv4 forwarding in one of the Linux systems. Which of the following commands can be used together to accomplish this task? (Choose two.)